The 10 biggest in-transit risks facing the AI infrastructure supply chain

AI hardware has become the most valuable — and most targeted — cargo moving through global supply chains today. A single GPU rack can carry more value than a full truckload of pharmaceuticals. A containerized data centre can represent hundreds of millions of dollars in computing power. And unlike traditional high-value cargo, AI infrastructure is also strategically significant: it determines which nations, corporations, and research institutions have access to
the intelligence that will define the next decade of economic and geopolitical competition. That combination of financial value, strategic consequence, and physical mobility makes AI hardware uniquely exposed to in-transit risk. And the threat landscape is evolving faster than most shippers realize.
A threat landscape under pressure
The numbers tell a stark story. Global cargo crime now costs businesses in excess of $18 billion annually, with the financial impact of individual theft events rising sharply as criminals increasingly target higher-value freight. There have been more than 2400 incidents reported in North America alone with $304k the average loss per cargo theft incident. The tactics being deployed — GPS spoofing, fraudulent documentation, front-company diversion — are growing in sophistication at pace with the value of the cargo being targeted.
For AI hardware specifically, the risks extend far beyond opportunistic theft. The U.S. Department of Justice launched Operation Gatekeeper in December 2025, disrupting the attempted export of over $160 million in AI chips to mainland China and Hong Kong in a single enforcement action. The Bureau of Industry and Security (BIS) increased its FY2026 enforcement budget by 23%, with funding specifically earmarked for semiconductor-related investigations. Export control violations, document fraud, and supply chain diversion have become industrial-scale operations — and AI hardware sits at the centre of them.
Meanwhile, hyperscalers, OEMs, and infrastructure builders must maintain continuous visibility and compliance to avoid export-licence revocation and reputational damage. The challenge is clear: protect AI infrastructure whilst in motion, and achieve asset visibility and chain-of-custody certainty across a multi-carrier, multi-country, high-value supply chain.
The top 10 in-transit risks
Based on intelligence from enforcement actions, industry data, and global supply chain operations, these are the ten risks every AI hardware shipper needs to understand:
1. Organized cargo theft — Coordinated criminal networks targeting GPU and server shipments
2. Smuggling & diversion — Hardware rerouted to restricted countries via falsified routing
3. Export control violations — Non-compliance with BIS (Bureau of Industry and Security) rules triggering seizure and penalties
4. BOL fraud — Fake or manipulated Bills of Lading (BOL: legal contract between shipper and carrier) enabling unauthorized delivery
5. Transit damage — Fragile AI hardware destroyed by mishandling or environmental failure
6. State-sponsored espionage — Nation-state actors intercepting or tampering in transit
7. Visibility gaps — No real-time tracking across multi-modal, cross-border routes
8. Counterfeit components — Substituted or downgraded hardware accepted at delivery
9. Last-mile vulnerabilities — Edge and remote deployments with minimal physical security
10. Destination non-compliance — Failure to verify end-use at delivery triggers enforcement
These risks don't operate in isolation. The most sophisticated schemes combine multiple vectors simultaneously — layering document fraud over physical diversion while exploiting visibility gaps to avoid detection. Understanding them individually is the first step; understanding how they interact in practice is what separates reactive shippers from resilient ones.

The anatomy of a supply chain breach
Three categories deserve particular attention. First, export control compliance has transformed from a paperwork exercise into a live operational risk. The regulatory environment around AI hardware is shifting rapidly — BIS has expanded Entity List designations, tightened licensing requirements, and significantly increased its enforcement posture. Companies operating across borders face a compliance landscape where the rules can change faster than shipment
documentation can be updated.
Second, BOL fraud and identity deception have become the preferred vectors for high-value diversion. Modern freight fraud rarely involves physical interception; instead, perpetrators infiltrate the documentation layer — creating parallel paper trails that route cargo to unintended destinations while appearing compliant at every checkpoint. Without verified chain of custody at each handoff point, shippers often don't know something has gone wrong until the hardware has already left their control entirely.
Third, visibility gaps remain the systemic vulnerability that enables everything else. Siloed tracking systems, manual check-ins, and basic ETA updates are not adequate for cargo of this consequence. When a shipment crosses four carriers, three countries, and two transshipment ports, real-time, multi-modal visibility isn't a luxury — it's the foundation of any meaningful risk strategy.
The Super Micro case: a warning for the industry
In March 2026, the indictment of Super Micro Computer co-founder Yih-Shyan "Wally" Liaw provided the industry with its clearest illustration yet of how these risks converge in practice. Liaw and two co-conspirators were charged with conspiring to divert approximately $2.5 billion in Nvidia AI servers to China in violation of U.S. export control laws — making it one of the largest technology smuggling cases in history.
The mechanics of the scheme were instructive. A Southeast Asian company served as the declared end buyer, placing purchase orders with Supermicro as legitimate business. Servers were shipped to Taiwan, transferred to the Southeast Asian entity, then stripped of identifying packaging and forwarded to China in unmarked boxes. To avoid triggering internal compliance alerts, the conspirators physically staged thousands of dummy servers at the declared warehouse — complete with serial numbers transferred between real and fake hardware using a hairdryer. The scheme allegedly ran for over a year before federal investigators intervened.
What this case demonstrates is not a flaw in any single process, but a failure across the entire chain: falsified documentation, a front entity exploiting visibility gaps, no meaningful end-use verification, and physical sleight of hand at the warehouse level. Six of the ten risks in our framework were present in this single case. Super Micro shares fell 33% on the day of the indictment, erasing over $6 billion in market value — a measure of just how consequential these failures can be.
How Overhaul addresses these risks
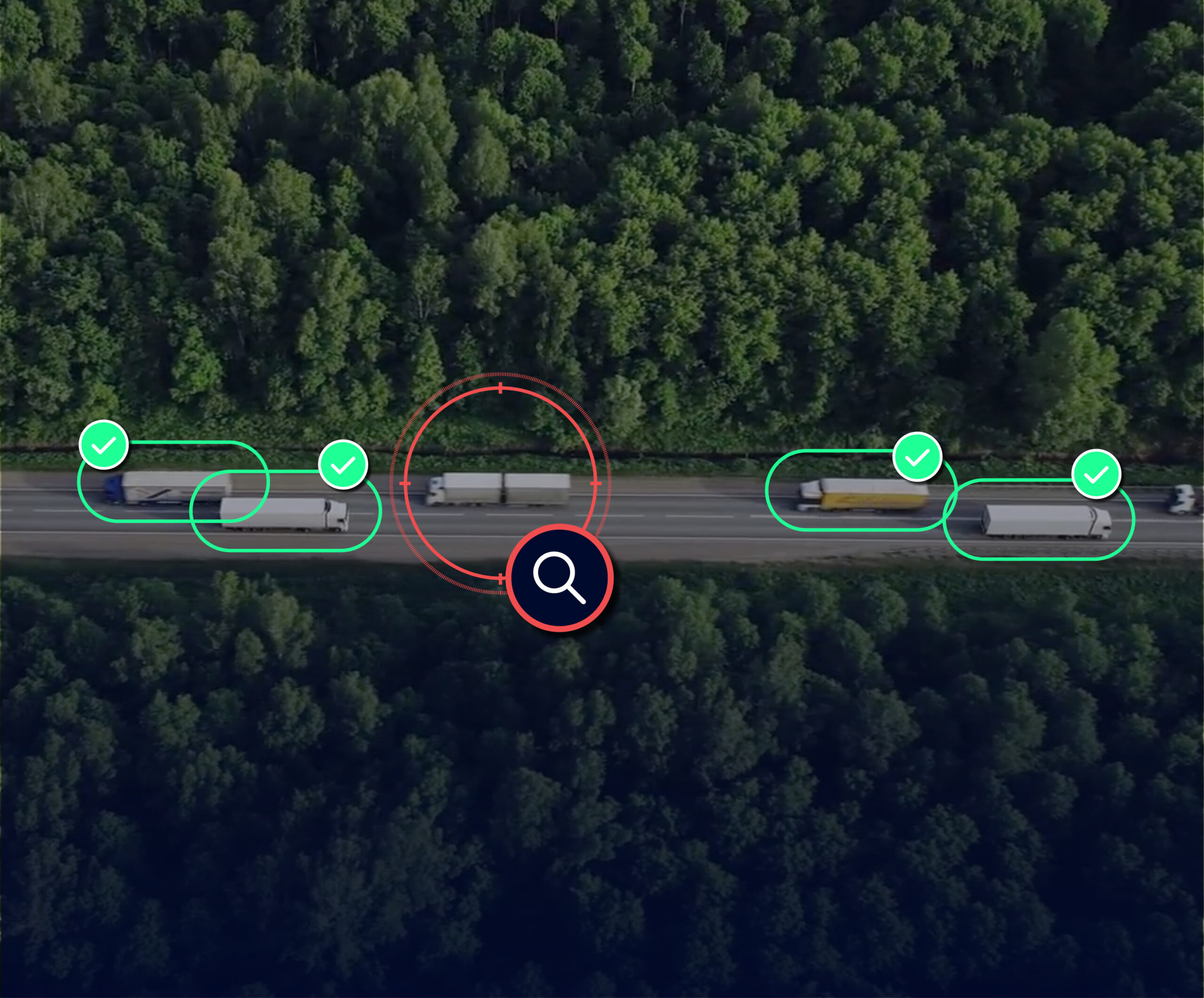
The shippers navigating this environment successfully share one common characteristic: they treat in-transit risk as an operational function, not a compliance checkbox. That means real-time visibility across every mode and every mile, chain-of-custody verification at every handoff, and the capacity to respond when risk materialises — not just report on it after the fact.
Overhaul's AI Asset Protection Solution is purpose-built for this challenge, bringing together two powerful tools that address these ten risks across the full lifecycle of AI hardware — from first dispatch to final deployment.
Risk Monitor: protecting AI infrastructure in motion
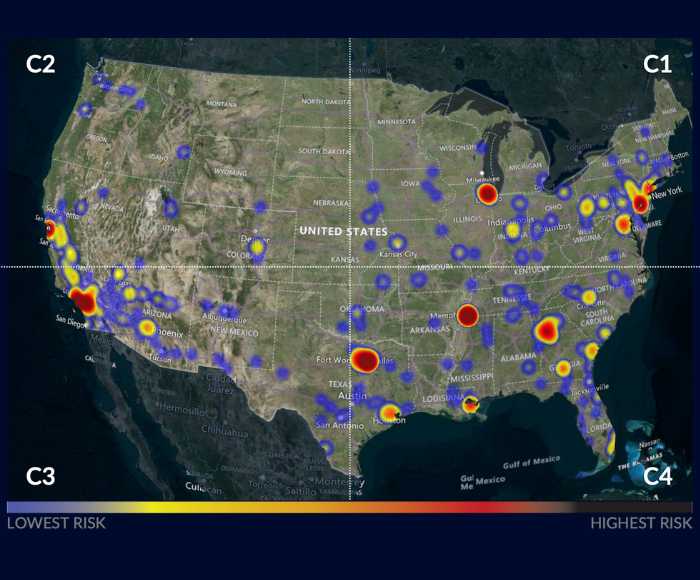
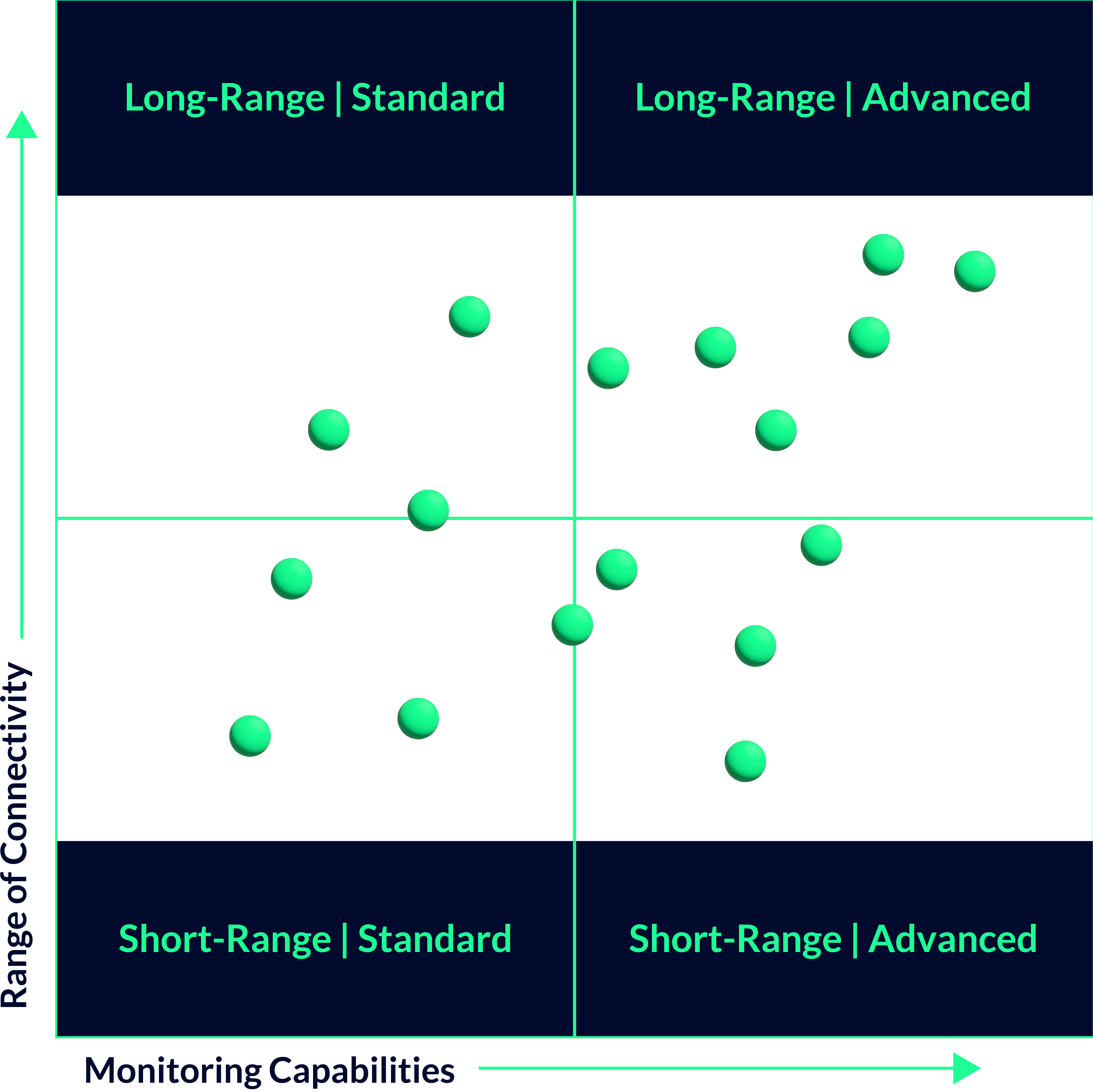
Risk Monitor provides real-time, in-transit visibility and proactive event response for every AI hardware shipment in your supply chain. It directly addresses the risks of cargo theft, visibility gaps, smuggling and diversion, and export control violations through:
1. Global shipment visibility: Track every AI hardware shipment worldwide from a single unified view, eliminating the blind spots that sophisticated diversion schemes exploit.
2. Risk prioritization: Dynamic, AI-driven risk scoring instantly focuses attention on the highest-risk shipments — so your team responds to what matters most, faster.
3. Proactive alerts: Detect route deviations, unauthorized access, and high-risk stops before they escalate into theft, tampering, or compliance failures.
4. Automated compliance: Ensure every shipment meets your standards of care without manual oversight — critical for maintaining export-licence integrity across complex multi-carrier routes.
5. Rapid response: Immediate context on risk drivers means faster, smarter decisions when seconds count.
Asset Manager: protection beyond delivery
Risk doesn't end at the destination. Asset Manager extends protection into the post-delivery phase — managing chain of custody, compliance, and asset integrity from arrival through deployment, returns, and repairs. It directly addresses last-mile vulnerabilities, destination non-compliance, transit damage, and counterfeit component risks through:
1. End-to-end asset tracking: Maintain full visibility from arrival through deployment, returns, and repairs — so nothing moves without a verified record.
2. Compliance safeguards: Automatically escalate if assets enter restricted zones or violate export controls, protecting your export licence and chain-of-custody requirements at every step.
3. Environmental assurance: Monitor temperature, shock, and humidity to prevent damage and prove proper handling — critical for fragile GPU and server infrastructure.
4. Secure reverse logistics: Verify custody at every step of the return journey, maintaining the integrity of your compliance record.
5. Integrated recovery: Activate rapid response for theft or compliance breaches through your preferred channels, minimising exposure when incidents occur.
Together, Risk Monitor and Asset Manager form the defence system for the world's highest value, highest consequence cargo — providing continuous, real-time command over AI hardware so nothing moves without you knowing.
The threat landscape facing AI infrastructure is real, it is growing, and it is sophisticated. The question for every shipper is whether their risk posture is keeping pace.
Learn more about how Overhaul protects AI hardware supply chains.